
Master Exposure Window Precision
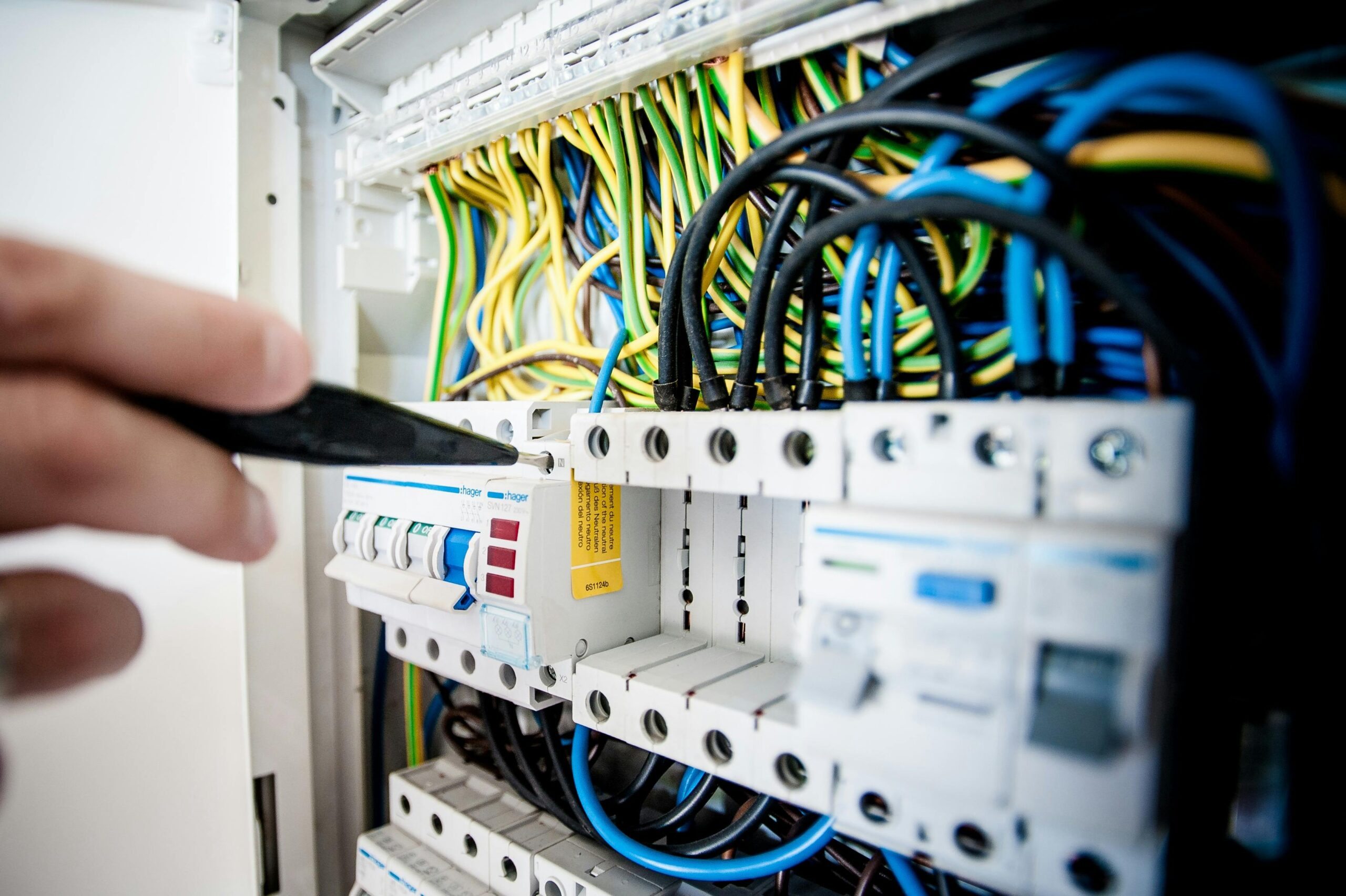
Understanding exposure window identification is crucial for professionals seeking to enhance accuracy and workflow optimization across industries ranging from photography to

Understanding exposure window identification is crucial for professionals seeking to enhance accuracy and workflow optimization across industries ranging from photography to

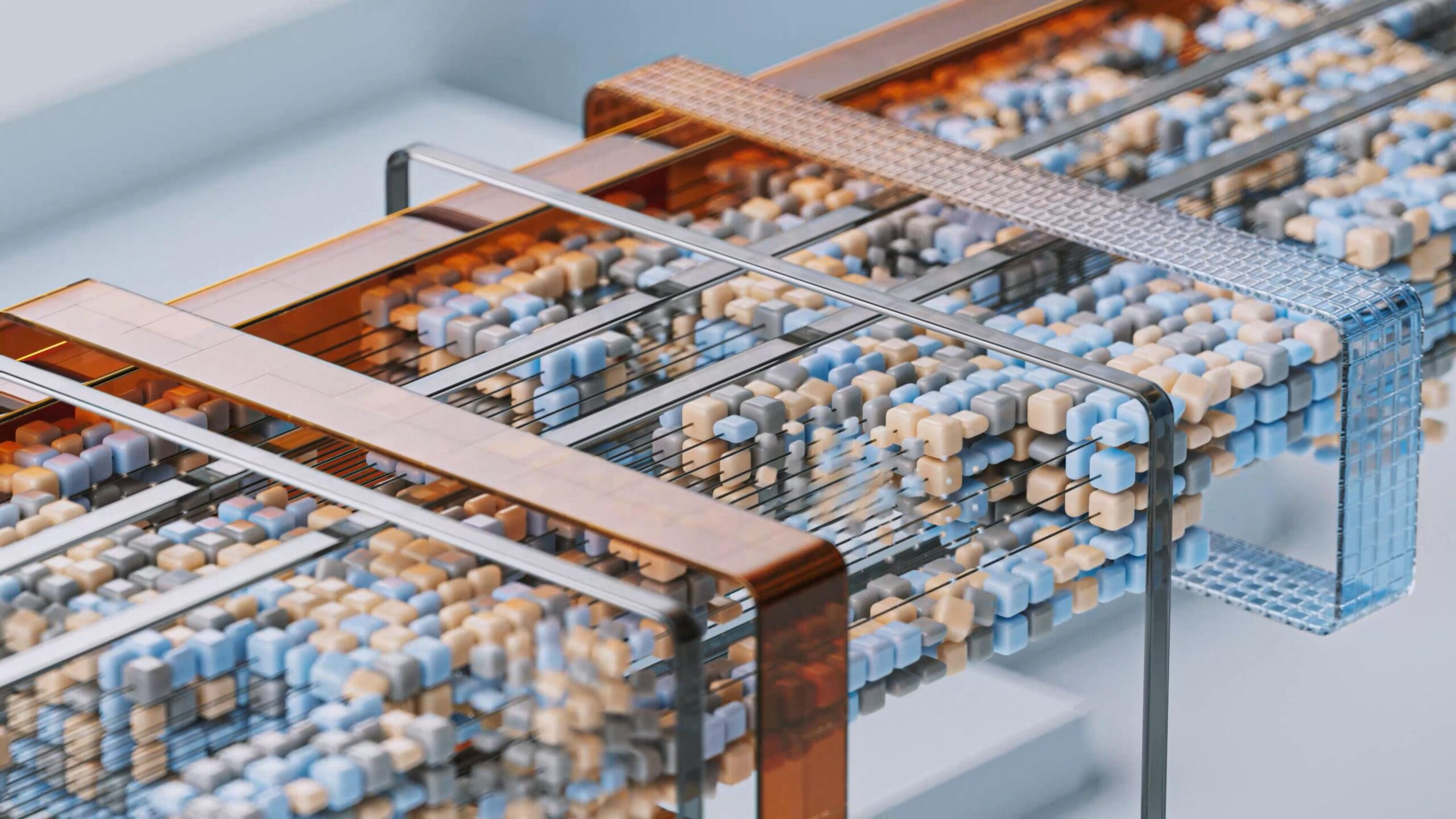
Managing cryptographic keys throughout their entire lifecycle is essential for maintaining robust security and ensuring seamless data protection across modern digital

Operational handoffs represent critical moments where success or failure is determined. When teams master these transition points, organizations unlock unprecedented efficiency
Mastering key storage and retrieval flow is essential for modern businesses seeking to balance robust security with seamless operational efficiency. In
The digital era demands constant evolution. Organizations and individuals alike must navigate complex systems where outdated processes can hinder progress, making
Understanding how different elements of your projects connect is crucial for success. Key dependency relationship mapping transforms chaos into clarity, enabling

Discover how tracking your keyboard key usage frequency can transform the way you work, offering deep insights into your typing habits

Key rotation stands as one of the most critical yet often overlooked security practices in modern infrastructure management, demanding strategic scheduling

Managing cryptographic keys effectively is one of the most critical yet overlooked aspects of modern cybersecurity infrastructure that directly impacts your

Cryptographic key management stands as the cornerstone of modern digital security, protecting everything from online banking to government communications across the