
Resilience Unlocked: Measuring Partial Key Exposure
In an era where digital security faces unprecedented challenges, understanding how cryptographic systems withstand partial compromises has become crucial for protecting

In an era where digital security faces unprecedented challenges, understanding how cryptographic systems withstand partial compromises has become crucial for protecting

In today’s digital landscape, brute-force attacks remain one of the most persistent cybersecurity threats facing organizations and individuals worldwide. Understanding how

Cryptographic security relies on robust hash functions and message authentication codes (MACs) that resist sophisticated attacks. Understanding resistance metrics is fundamental

Understanding and measuring resistance metrics has become essential in today’s interconnected world, where vulnerabilities can lead to catastrophic consequences across industries

Cloud computing has revolutionized business operations, but with great power comes great responsibility. Understanding and managing lifecycle risks is essential for
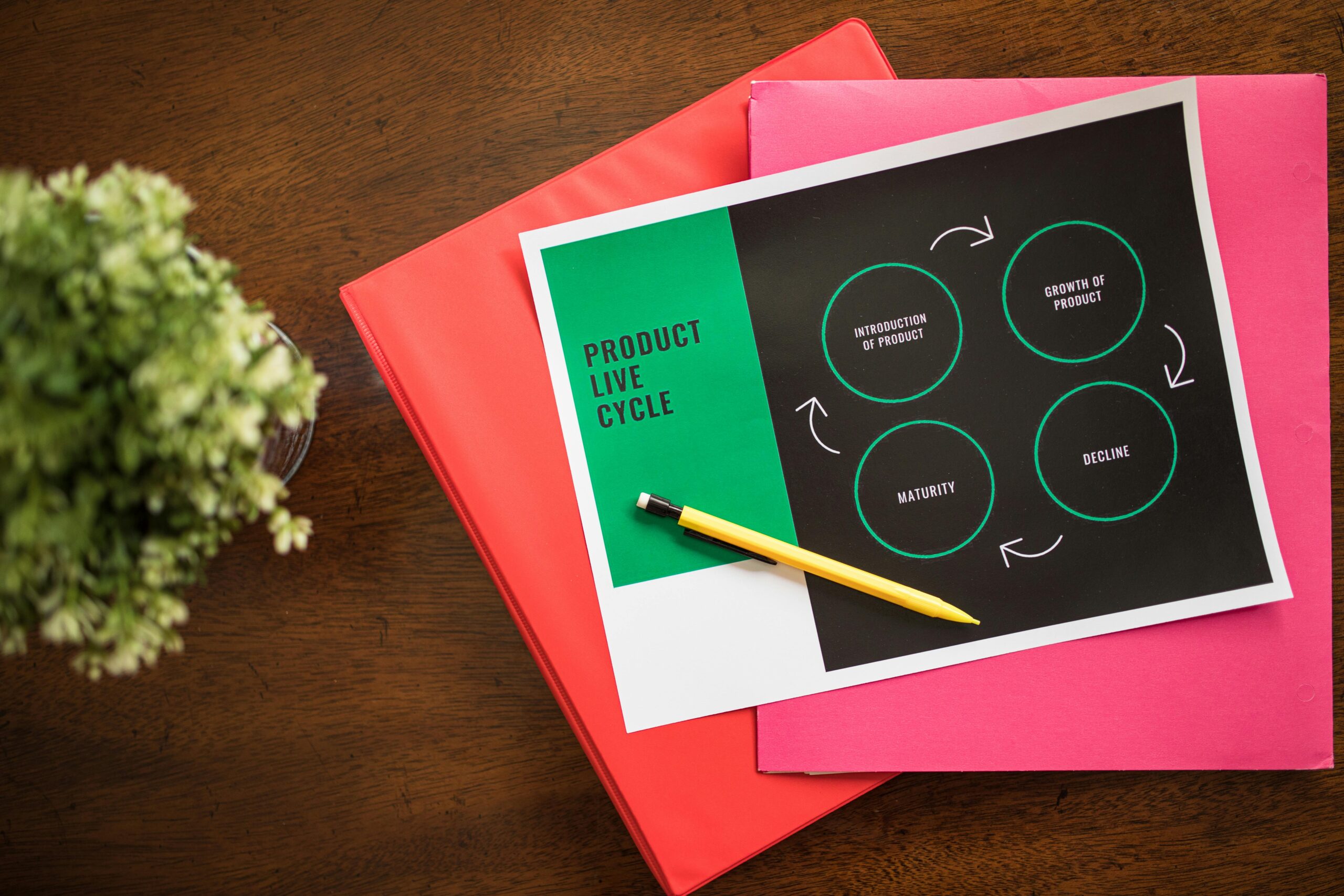
Understanding and mapping key lifecycles isn’t just a business practice—it’s a strategic imperative that separates thriving organizations from those struggling to

Multi-tenant systems have become the backbone of modern cloud computing, serving multiple customers from a single infrastructure while maintaining strict isolation

In today’s digital landscape, cryptographic keys serve as the foundation of secure communications, data protection, and authentication systems across every connected

Key-cycle mapping has emerged as a transformative approach in organizational management, enabling companies to prevent costly incidents while dramatically improving operational

Hardware-backed cryptographic keys represent the cornerstone of modern security architecture, offering unparalleled protection through dedicated security modules like HSMs and TPMs.