Conquering Constraints
Change is never easy, especially when organizations face implementation constraints that can derail even the most promising initiatives. 🚀 In today’s
Change is never easy, especially when organizations face implementation constraints that can derail even the most promising initiatives. 🚀 In today’s

Understanding security research papers is essential for professionals navigating the complex landscape of cybersecurity claims, threat models, and technical validation methods.

Downgrade attacks represent one of the most insidious threats to modern network security, silently forcing systems to use weaker encryption protocols

Standardization in resistance measurement transforms technical workflows by eliminating variability, reducing errors, and ensuring consistent, reliable results across laboratories and industries

Understanding how resistance metrics shape algorithm performance is crucial for making informed decisions in machine learning and data science projects today.

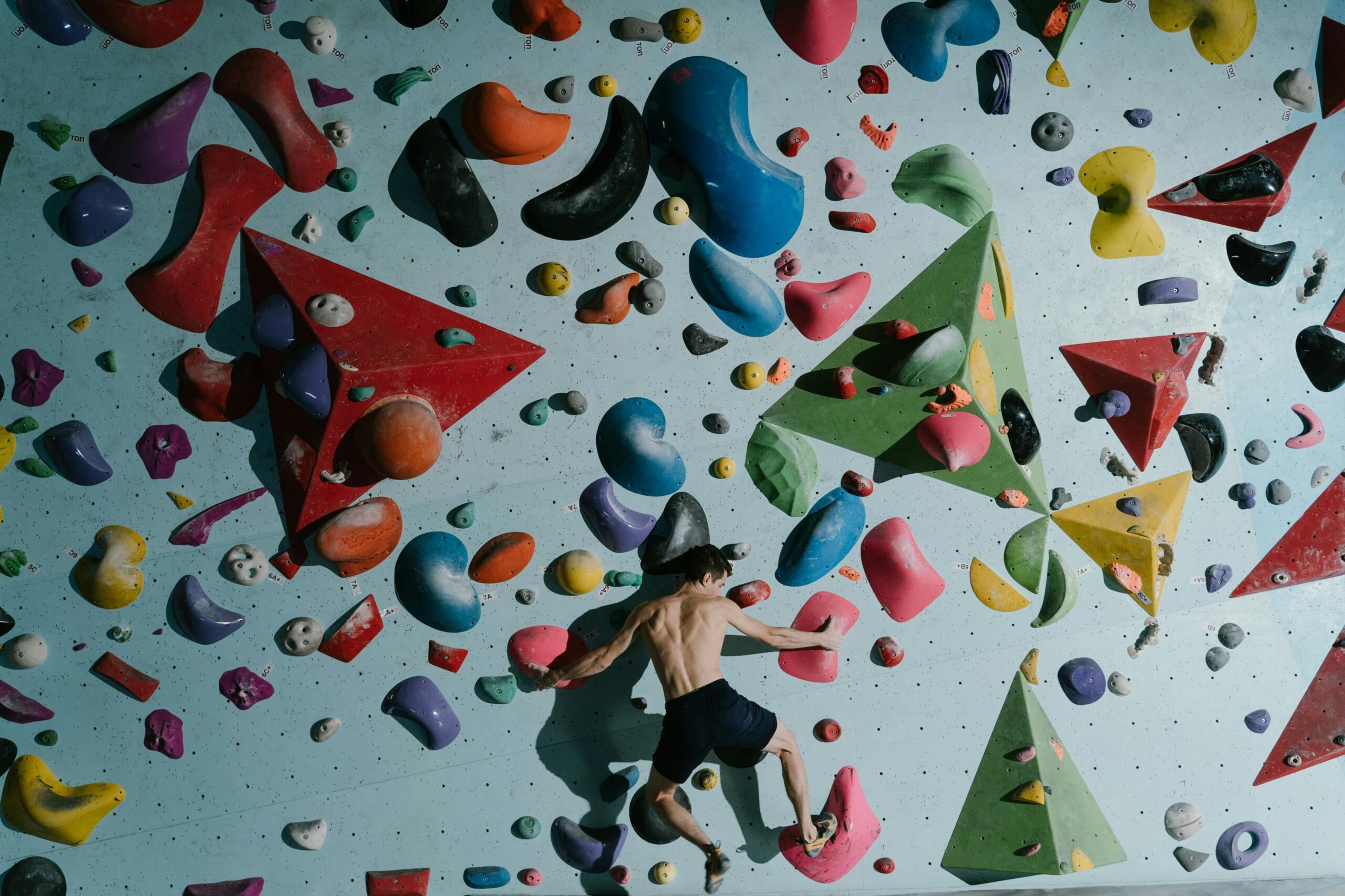
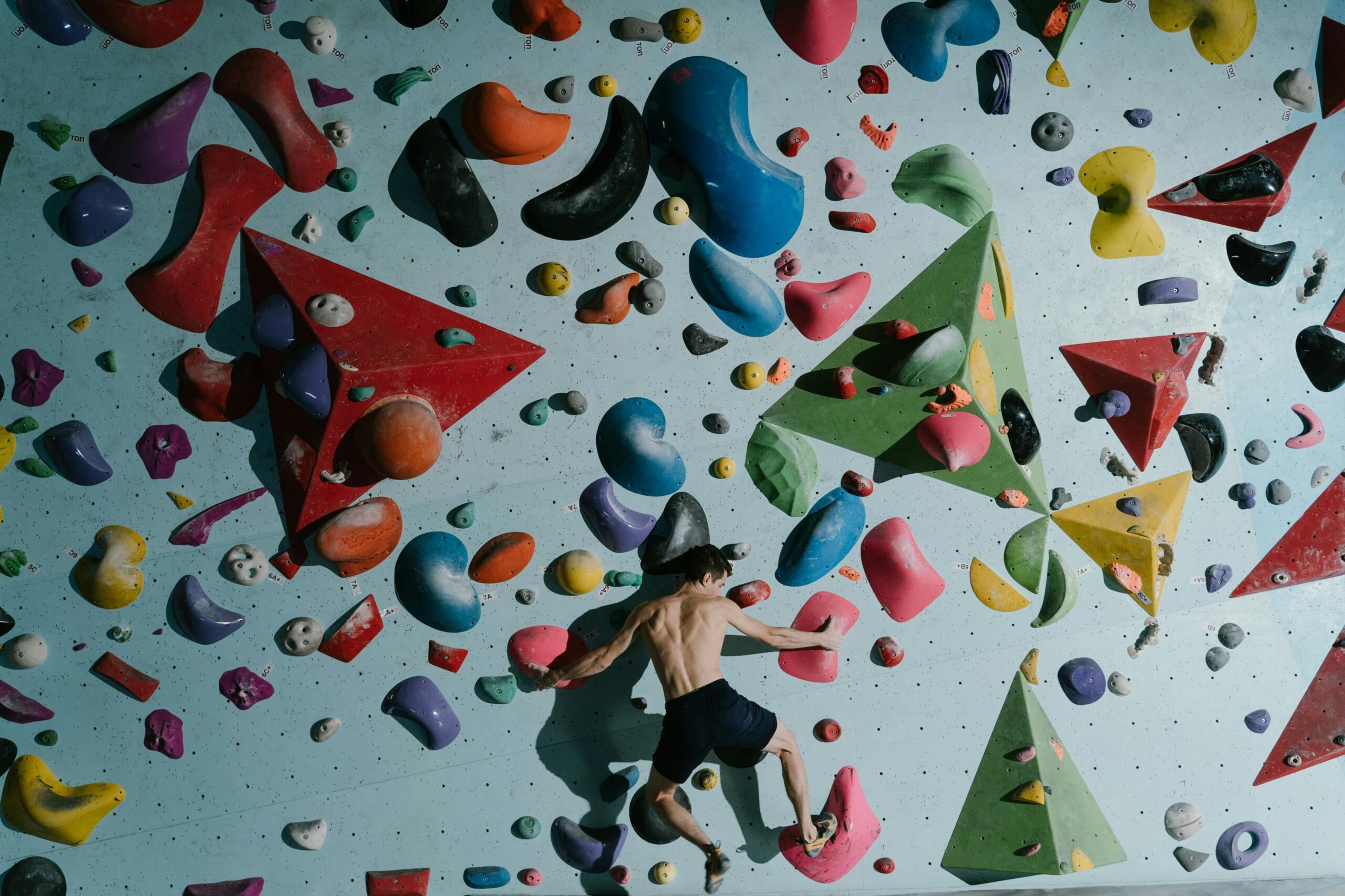
Performance optimization requires a delicate balance between resistance and energy expenditure. Whether in athletics, electronics, or daily productivity, finding this equilibrium

Defining resistance metrics is one of the most underestimated yet critical components of business strategy development that can make or break

Adversarial cost models represent a critical frontier in cybersecurity, where understanding attacker economics becomes essential for building resilient defenses against evolving

Side-channel attacks exploit physical implementation characteristics of cryptographic systems, threatening even mathematically secure algorithms through observable phenomena like power consumption and

Algorithm performance varies dramatically when subjected to competitive pressure, revealing hidden strengths and weaknesses that standard testing often misses completely. 🔍